Generic SSO Setup |
Configure SSO service provider
Prerequisites in Sage People:
-
If required, set up a custom Salesforce domain before setting up the SSO
-
If both single sign-on and logging in with a username and password are required—typically, SSO for active employees and logging in with a username and password on the org's login page for pre boarders—then the Salesforce org domain must be my.salesforce.com
-
In the SSO service provider, create the app for users to access the Sage People org.
- Select Configure Single Sign-On.
- Choose SAML-based Sign-on from the picklist.
- Enter your Sage People org’s Salesforce URL in both Identifier and Reply URL fields. (The system can also refer to one of these as Entity ID).
Tip
G-Suite requires an ACS URL. You can take this from the Sign On URL that Salesforce provides after completing the Salesforce steps below. When first creating the SSO app, enter the org domain URL and update this later.
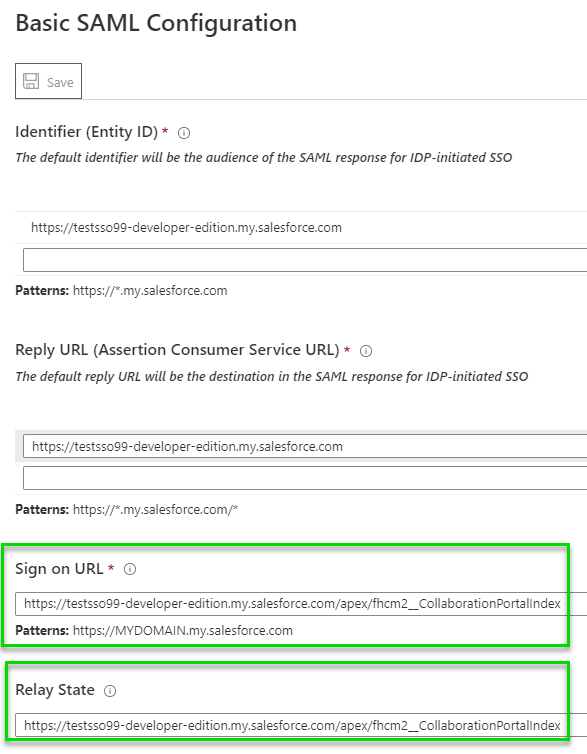
- Configure your single sign-on provider to direct team members signing in to WX:
Enter your Sage People org’s WX URL in Sign on URL or Start URL:
https://xxx.my.salesforce.com/apex/fhcm2__CollaborationPortalIndex. Replacexxx.my.salesforce.comwith the org's custom domain.- Enter your Sage People org’s WX URL in Relay State (where applicable):
https://xxx.my.salesforce.com/apex/fhcm2__CollaborationPortalIndex. Replacexxx.my.salesforce.comwith the org's custom domain.
NoteIn Okta, Default Relay State is simply
/apex/fhcm2__CollaborationPortalIndexas shown in the screenshot. Okta doesn’t require a full string. This is because it passes the relay state end-point URL in the SAML assertion: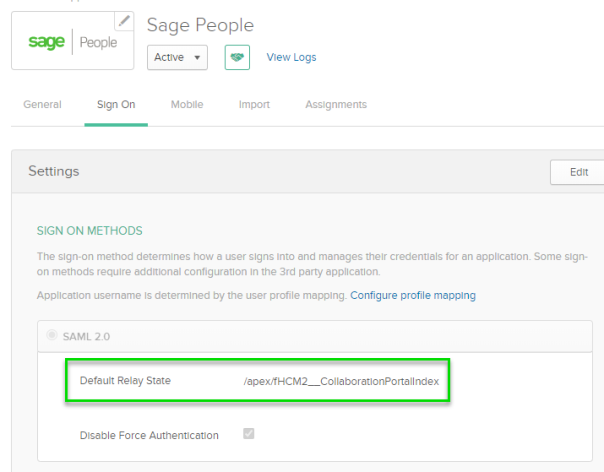
In Azure, enter the Sign On URL and Relay State as shown in the screenshot. You need to configure both the Relay State and the Sign on URL in full in Azure. This forces the user to WX:
- Copy and note the custom metadata link.
- Download the certificate and save.
- Select Save.
- Provision the app to all users who require access to it.